Compliance with HIPAA, NIST, and PCI-DSS: A Practical Guide for Growing Businesses
If you handle patient data, process credit cards, or work with federal or enterprise clients, you’re already in the world of HIPAA, NIST, and PCI-DSS — the challenge is staying compliant without slowing your business down.
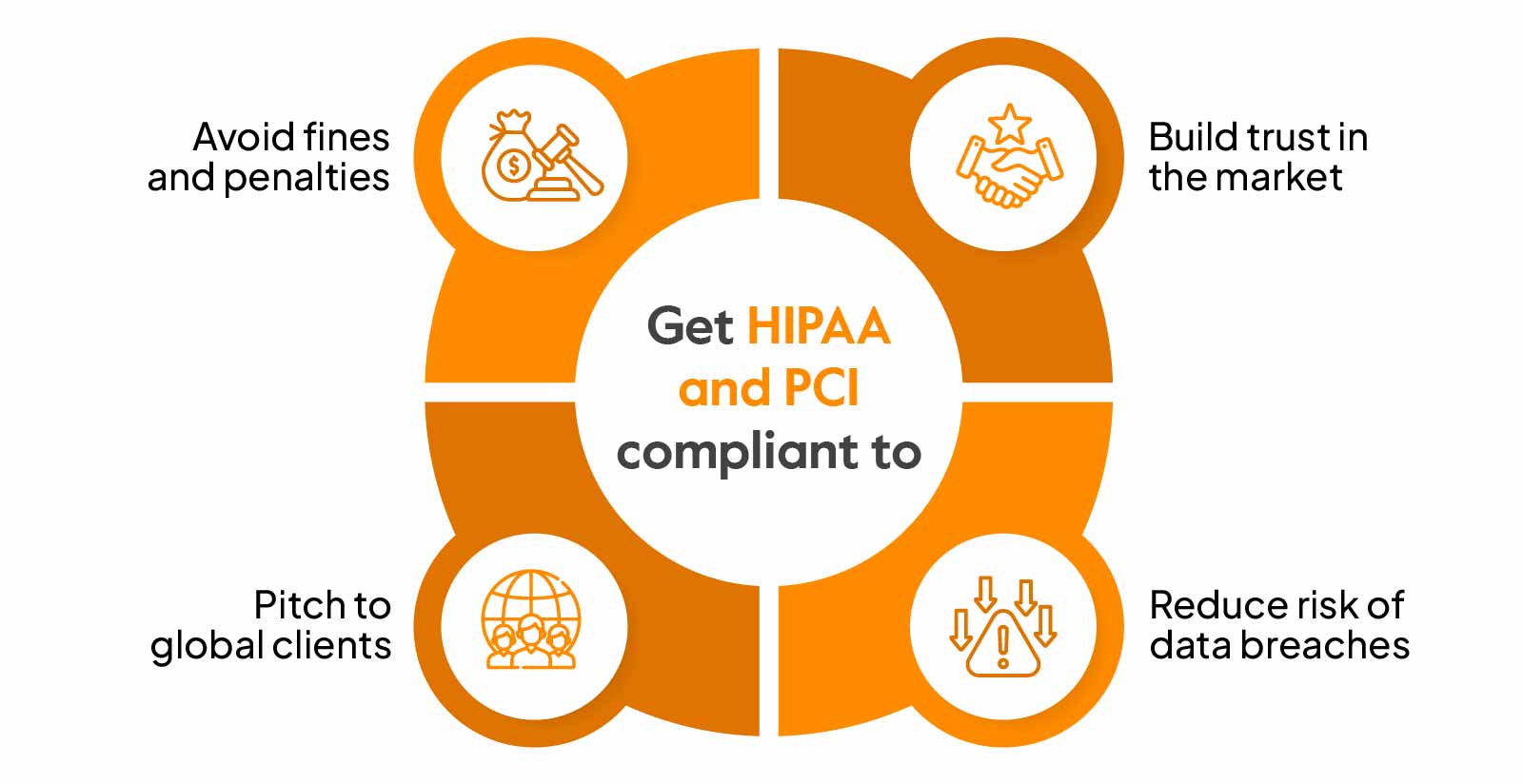
Regulations and security frameworks can feel overwhelming, especially if you’re running a fast-moving business. But here’s the truth: HIPAA, NIST, and PCI-DSS are more than checklists — they are proven ways to protect your business, your clients, and your reputation.
What Are HIPAA, NIST & PCI-DSS?
HIPAA – Protecting Patient Information
HIPAA applies to medical providers, billing firms, and IT vendors handling PHI.
- Controls access to patient data
- Requires secure systems & encryption
- Strict breach reporting rules
NIST – The Security Framework
NIST standards guide organizations in implementing modern cybersecurity controls.
- Often required for federal compliance
- Covers identification → protection → detection → response → recovery
PCI-DSS – Securing Card Payments
Any business accepting credit/debit cards must follow PCI rules.
- Secures POS, networks, and payment systems
- Reduces fraud & chargebacks
- Required for online and physical payments
Where These Standards Overlap
- Access control & authentication
- Monitoring & logging
- Encryption at rest & in transit
- Ongoing staff training
- Documented policies & procedures
One strong cybersecurity foundation supports all three frameworks.
How Districtconnects Helps You Stay Compliant
1. Compliance Readiness Assessment
- Gap analysis for HIPAA/NIST/PCI
- Asset & data flow mapping
- Risk scoring & recommendations
2. Secure Network Architecture
- Network segmentation
- Secure Wi-Fi (Guest / POS / PHI separation)
- Next-gen firewalls & VPN
3. Endpoint & Cloud Protection
- Managed antivirus/EDR
- Patch management
- Hardening Microsoft 365 & cloud apps
4. Monitoring & Incident Response
- 24/7 monitoring
- Centralized logging
- Incident response playbooks
5. Documentation & Training
- Policy creation
- Annual & onboarding training
- Audit-ready documentation
Ready to Strengthen Your Compliance?
Businesses should consider compliance when handling PHI, accepting card payments, or pursuing contracts requiring NIST readiness.
This article is for informational purposes only and not legal advice.
