Network Security • CCTV • Small Business
The Hidden Danger of Cheap Security Cameras: How Untrusted Brands Create Backdoors Into Your Network
Many businesses install low-cost, untrusted security cameras—often bought from Amazon, Costco, or random online marketplaces—without realizing they may be opening a backdoor into their entire network.
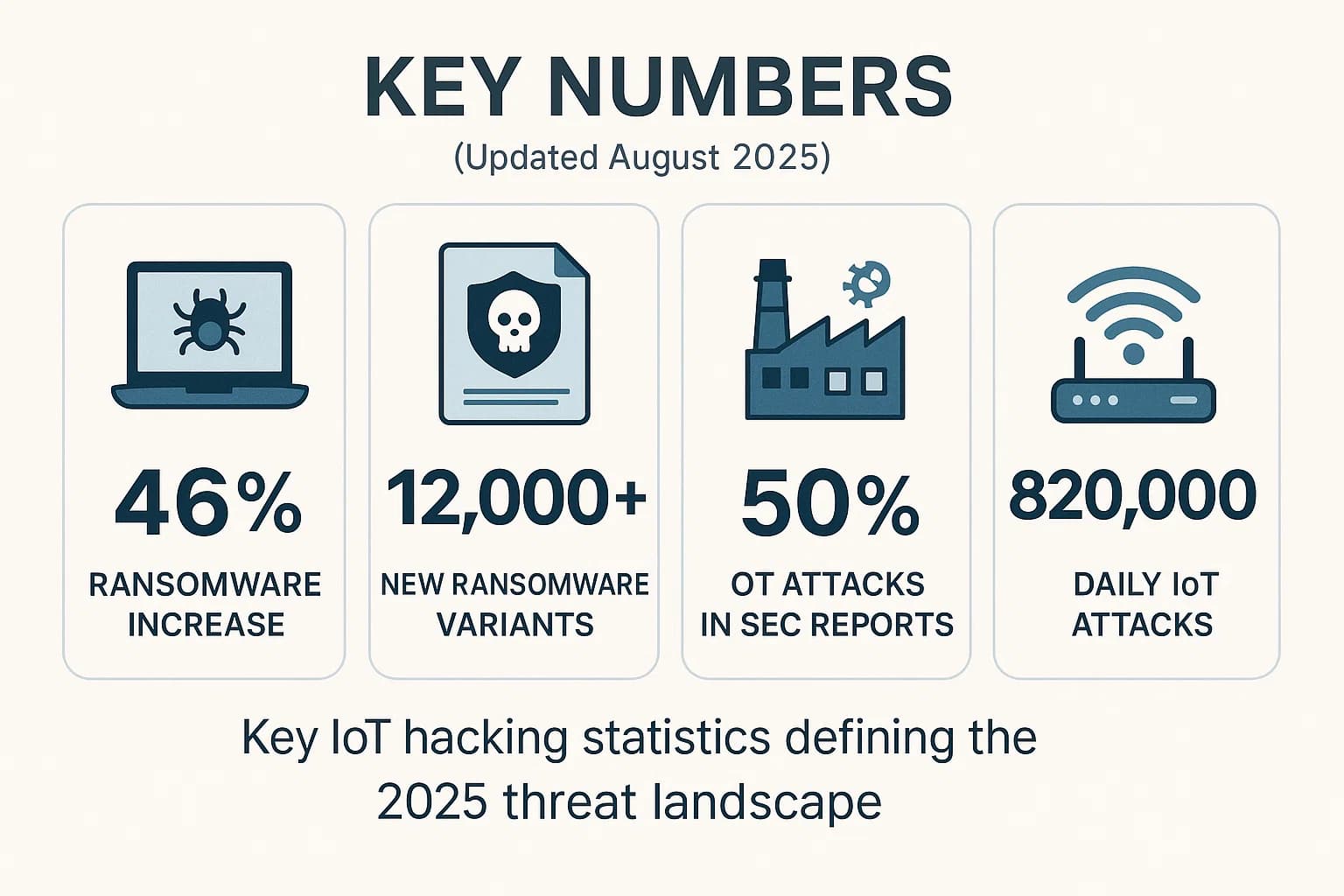
Research shows over 50% of IoT devices contain critical vulnerabilities, and one in three cyber breaches now involves an IoT device — including security cameras, NVRs, smart sensors, and access control systems.
Cheap Cameras, Big Risk: What Most Businesses Don’t See
Modern IP cameras are small, internet-connected computers. With unverified firmware, unknown cloud connections, and poor encryption, they offer attackers a perfect entry point into your internal network.
A compromised camera doesn’t just leak video — it can expose your entire business environment.
1. Unknown Firmware & Hidden Backdoors
- Outdated operating systems that never get patched
- Hard-coded admin accounts
- Hidden remote-access services listening on open ports
- Outbound traffic to unknown cloud servers
Attackers actively scan for these devices because they offer easy access into business networks.
2. Cameras Sitting on the Same Network as Your Business Systems
Most DIY installs plug cameras into:
- Same switch as POS systems
- Same LAN as employee laptops
- The main ISP modem/router
- Unmanaged PoE switches with zero security
If one cheap camera is compromised, attackers can pivot to:
- File servers
- QuickBooks & accounting systems
- POS terminals
- Microsoft 365 accounts
- Customer data
3. Insecure P2P Cloud Apps
Off-brand DVRs and NVRs often rely on “P2P cloud” mobile apps that route traffic through unknown foreign servers, storing device IDs, credentials, and video metadata offsite without transparency.
4. No Security Patching or Updates
Unknown brands rarely release firmware updates. Once vulnerabilities are discovered, you are permanently exposed with no fixes available.
How DistrictConnects Secures Your CCTV — The Right Way
✔ Trusted camera platforms only
No mystery firmware. No offshore servers. No unknown cloud apps.
✔ CCTV on a fully isolated VLAN
Cameras never touch your office computers, POS devices, guest Wi-Fi, or internal servers.
✔ Strict firewall rules
Outbound traffic is restricted, monitored, and blocked from talking to sensitive systems.
✔ Secure remote access
VPN-based or hardened firewall-published access only — never insecure cloud P2P apps.
Your Business Handles Real Client Data — Treat Cameras as Critical Infrastructure
Retail, manufacturing, professional services, medical, restaurants — every business stores sensitive data. A cheap camera should never be the doorway into your business.
Ready to Secure Your CCTV — Not Just Install It?
DistrictConnects designs and deploys secure, isolated, fully protected CCTV environments built for modern businesses.
Serving small and mid-sized businesses across Northern Virginia and the DMV.
